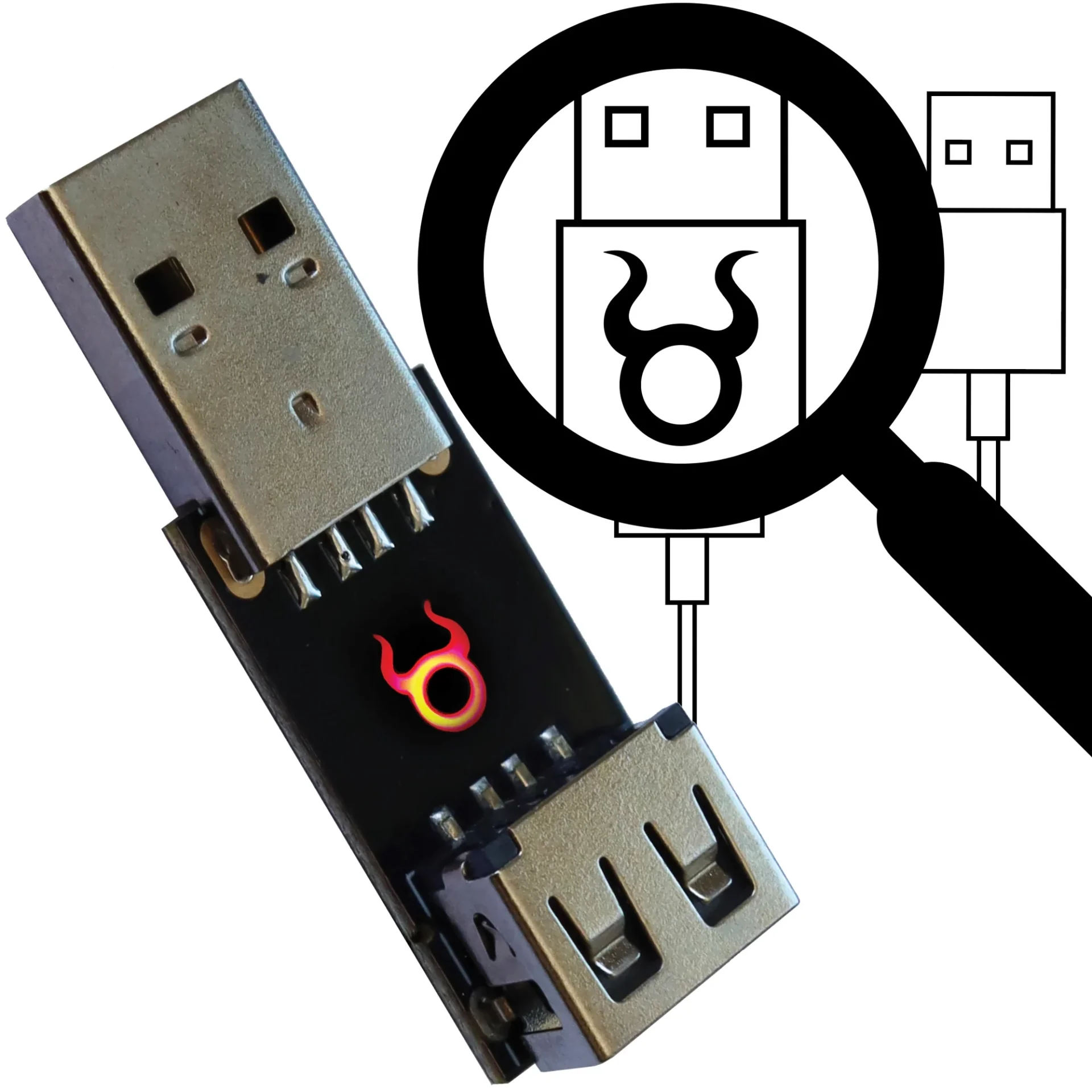
Cactus WHID: WiFi HID Injector USB (Rubberducky)
$29.69
$50.77
Cactus WHID: WiFi HID Injector USB Rubberducky On SteroidsWiFi HID Injector for Fun & Profit – An USB Rubberducky On Steroids. [ Customized HW based on Atmega 32u4 and ESP-12S.This device allows keystrokes to be sent via WiFi to a target machine. The target recognises the Ducky as both a standard HID keyboard and a serial port, allows interactive commands and scripts to be executed on the target remotely.WiFi HID Injector for Fun & Profit Hardware Design Author: Luca Bongiorni – https://twitter.com/lucabongiorni Initial sw based on ESPloit by Corey Harding of www.LegacySecurityGroup.com WHID Mobile Connector by Paul https://twitter.com/paulwebsechttps://ae-cn.alicdn.com/9f8e1de30350cb41/nvh3YLVcQnLuEd5kGXL/LAUN1FWiEIsHcWZ5bvm_306393367359_mp4_264_sd.mp4Third-Party Softwares Compatible with WHID’s Hardwarehttps://github.com/whid-injector/WHIDwhid.ninjahttps://github.com/sensepost/USaBUSehttps://github.com/spacehuhn/wifi_duckyhttps://github.com/basic4/WiDuckyhttps://m.youtube.com/channel/UCzh8wlTSYbdZCs__Djym5UQHOW TO START [Newbies Edition]Since July 2017 all Cactus WHID are delivered with pre-loaded ESPloitV2 and are ready to Plug-n-Hack ✌Thus, even if you are not an Arduino expert, you can immediately have fun!Just plug it in an USB port and connect to the WiFi network:SSID “Exploit”Password “DotAgency”Open a web browser pointed to “http://192.168.1.1”The default administration username is “admin” and password “hacktheplanet”.https://youtu.be/5WTrKvQbK9oFor cool payloads or more info check the Wiki or the Payloads directory.The HardwareUSB PinoutsIn order to make easier the process of weaponizing USB gadgets, you can solder the USB wires to the dedicated pinouts.The pin closer to USB-A is GND. The pins are:GNDD D-VCCDocumentation WIKII HEAVILY RECOMMEND TO READ IT ALL! https://github.com/whid-injector/WHID/wikiThird-Party Softwares Compatible with WHID’s Hardwarehttps://github.com/whid-injector/WHID/tree/master/ESPloitV2_whid (Improved version of WHID GUI, installed by default on Cactus WHID hardware)https://github.com/sensepost/USaBUSe (Dedicated software for AirGap bypass Vs Windows)https://github.com/spacehuhn/wifi_ducky (old software similar to ESPloitV2)Possible ApplicationsClassic: Remote Keystrokes Injection Over WiFiDeploy WHID on Victim’s machine and remotely control it by accessing its WiFi AP SSID. (eventually you can also setup WHID to connect to an existing WiFi network)Social Engineering: Deploy WHID inside an USB gadgetThe main idea behind it is to test for Social Engineering weaknesses within your target organization (e.g. DLP policy violations) and to bypass physical access restrictions to Target’s device. Usually, I create a fancy brochure (sample template https://github.com/whid-injector/WHID/tree/master/tools/Social_Engineering_Lures ) attached with a weaponized USB gadget and then use a common delivery carrier (e.g. UPS, DHL, FedEx).Video TutorialsMore Video on WHID’s Youtube Channel:https://www.youtube.com/channel/UCzh8wlTSYbdZCs__Djym5UQ/videosBlogposts about WHIDhttps://www.x90x90.net/hardware/2021/03/26/HID-Implants-for-the-electrically-challenged.htmlhttps://blog.rootshell.be/2018/05/22/evil-mouse-project/https://medium.com/@LucaBongiorni/whid-injector-how-to-bring-hid-attacks-to-the-next-level-b06a40b7df22Forensics Analysis of HID Offensive Implants from Societe Generale’s CERThttps://github.com/certsocietegenerale/Publications/blob/master/DFRWS EU19 - The Rise Of HID Devices.pdf
Implants, Remote Access & Malicious Usbs